Sophos Supports Shift to Hybrid Environments with New Generation of Remotely Managed Wi-Fi 6 Access Points
Sophos, a global leader in innovating and delivering cybersecurity as a service, today announced the Sophos AP6 Series to support…

Sophos, a global leader in innovating and delivering cybersecurity as a service, today announced the Sophos AP6 Series to support…

Sophos, a global leader in innovating and delivering cybersecurity as a service, today announced that it has uncovered how research contests run…

Sophos Retainer Cuts Red-Tape, Allowing Sophos Incident Responders to Quickly Investigate and Remediate Active Attacks Shorter Attacker Dwell Times Require…

Sophos, a global leader in innovating and delivering cybersecurity as a service, today released new findings on CryptoRom scams—a subset of pig butchering (sh?…
Sophos, a global leader in innovating and delivering cybersecurity as a service, has announced a new sectoral survey report, “The…

Sophos, a global leader in innovating and delivering cybersecurity as a service, today released its annual “State of Ransomware 2023 ” report,…

Sophos Adds Team of MDR Experts in Germany, Expanding Global Footprint of Security Operations Specialists Defenders Have Less Time to…

Sophos, a global leader in innovating and delivering cybersecurity as a service, today announced the promotion of Joe Levy to…

Sophos, a global leader in innovating and delivering cybersecurity as a service, today published a new survey report, “The State…

Sophos, a global leader in innovating and delivering cybersecurity as a service, today released new research on how the cybersecurity…
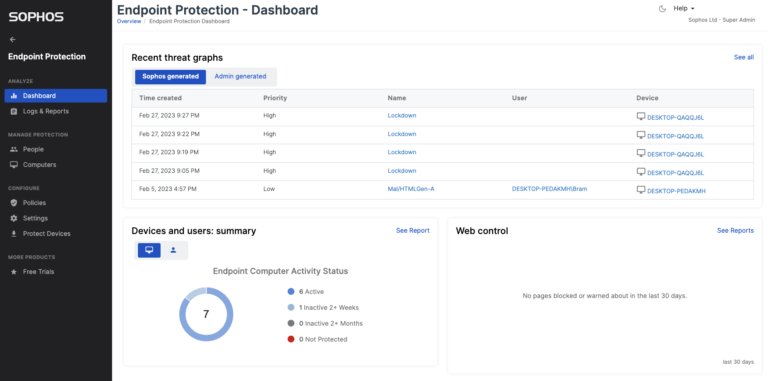
Sophos, a global leader in innovating and delivering cybersecurity as a service, today introduced innovative advancements to its portfolio of…

Sophos, a global leader in innovating and delivering cybersecurity as a service, today announced the expansion of its next-generation firewall portfolio with two new…

Sophos, a global leader in innovating and delivering cybersecurity as a service, today released details of two expansive, still operational,…
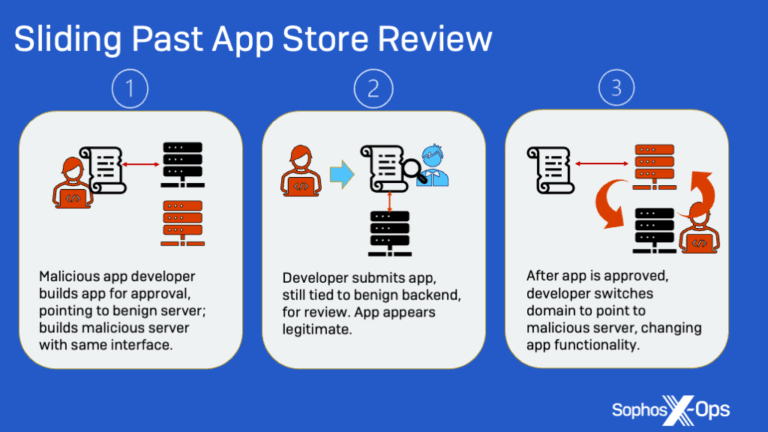
Sophos, a global leader in innovating and delivering cybersecurity as a service, today released new findings on CryptoRom scams—elaborate financial fraud schemes that prey…

Sophos, a global leader in innovating and delivering cybersecurity as a service, today announced that its Sophos Intercept X Advanced with XDR solution has…

Sophos, a global leader in innovating and delivering cybersecurity as a service, has announced the appointment of Gerard Allison as its Senior Vice President…

· Introduces Sophos Marketplace and $1 Million Breach Protection Warranty · Sophos X-Ops Identifies LockBit 3.0 Similarities to BlackMatter; Attackers Use Pentesting…

Sophos, a global leader in innovating and delivering cybersecurity as a service, today published findings of a new survey, “The…

Sophos, a global leader in innovating and delivering cybersecurity as a service, today published its 2023 Threat Report. The report details…

Sophos, a global leader in innovating and delivering cybersecurity as a service, today launched new third-party security technology compatibilities with Sophos Managed Detection…

08.09.2022 – Sophos, a global leader in next-generation cybersecurity, today published a new sectoral survey report, The State of Ransomware in Retail 2022,…

Sophos, a global leader in next-generation cybersecurity, has announced Sophos X-Ops, a new cross-operational unit linking SophosLabs, Sophos SecOps and Sophos…
Sophos, a global leader in next-generation cybersecurity, has published a new sectoral survey report, The State of Ransomware in Education 2022….

Sophos, a global leader in next-generation cybersecurity, has published a new sectoral survey report, “The State of Ransomware in Healthcare 2022.”…

OXFORD June 8, 2022 – Sophos, a global leader in next-generation cybersecurity, today released the “Active Adversary Playbook 2022,” detailing attacker…

Sophos, a global leader in next-generation cybersecurity, today announced it has been named a leader in the 2022 KuppingerCole Leadership Compass for…
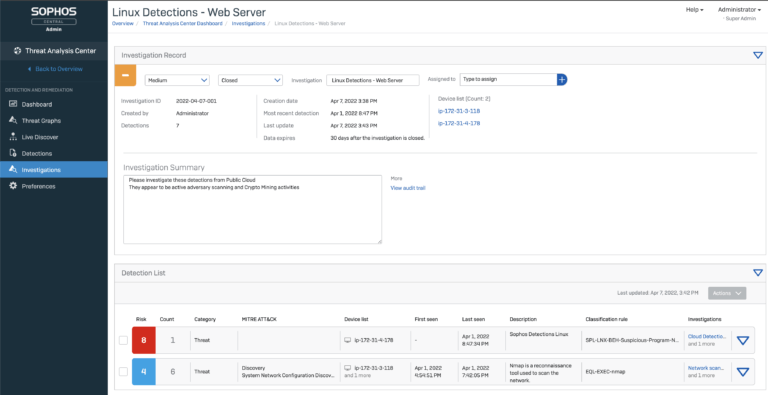
OXFORD, U.K. – April 14, 2022 – Sophos, a global leader in next-generation cybersecurity, todayunveiled advancements to Sophos Cloud Workload Protection,…

OXFORD, U.K. – March 31, 2022 – Sophos, a global leader in next-generation cybersecurity, has released findings on how attackers are using…
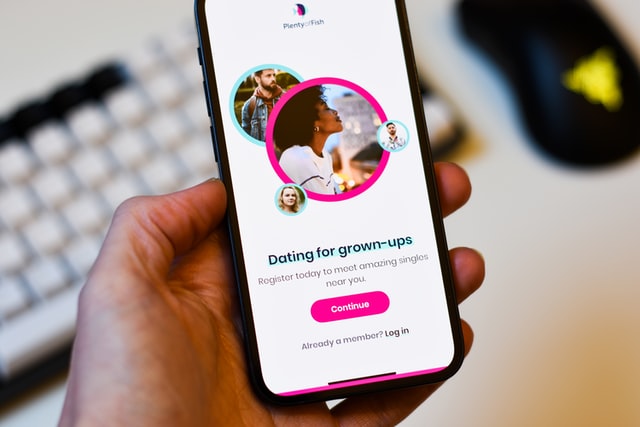
Sophos, a global leader in next-generation cybersecurity, has released new insight into an international cryptocurrency trading scam called CryptoRom that targets…

Sophos, a global leader in next-generation cybersecurity, today released findings of a dual ransomware attack where extortion notes left by Karma ransomware…